In modern data architecture, the reliability of information depends on the structural safeguards built into the design phase. Data integrity is not an afterthought; it is the foundation of trustworthy systems. When designing an Entity Relationship Diagram (ERD), the goal is to create a blueprint that inherently prevents corruption, inconsistency, and loss. By applying strict constraints, architects ensure that the database behaves predictably under load and across transactions.
Without these enforced rules, data becomes susceptible to human error, application bugs, and concurrent access issues. A well-structured ERD acts as a contract between the application logic and the storage layer, defining what is permissible and what is forbidden. This article details the mechanisms for maintaining consistency through rigorous design principles.
Understanding the Layers of Data Integrity 🔍
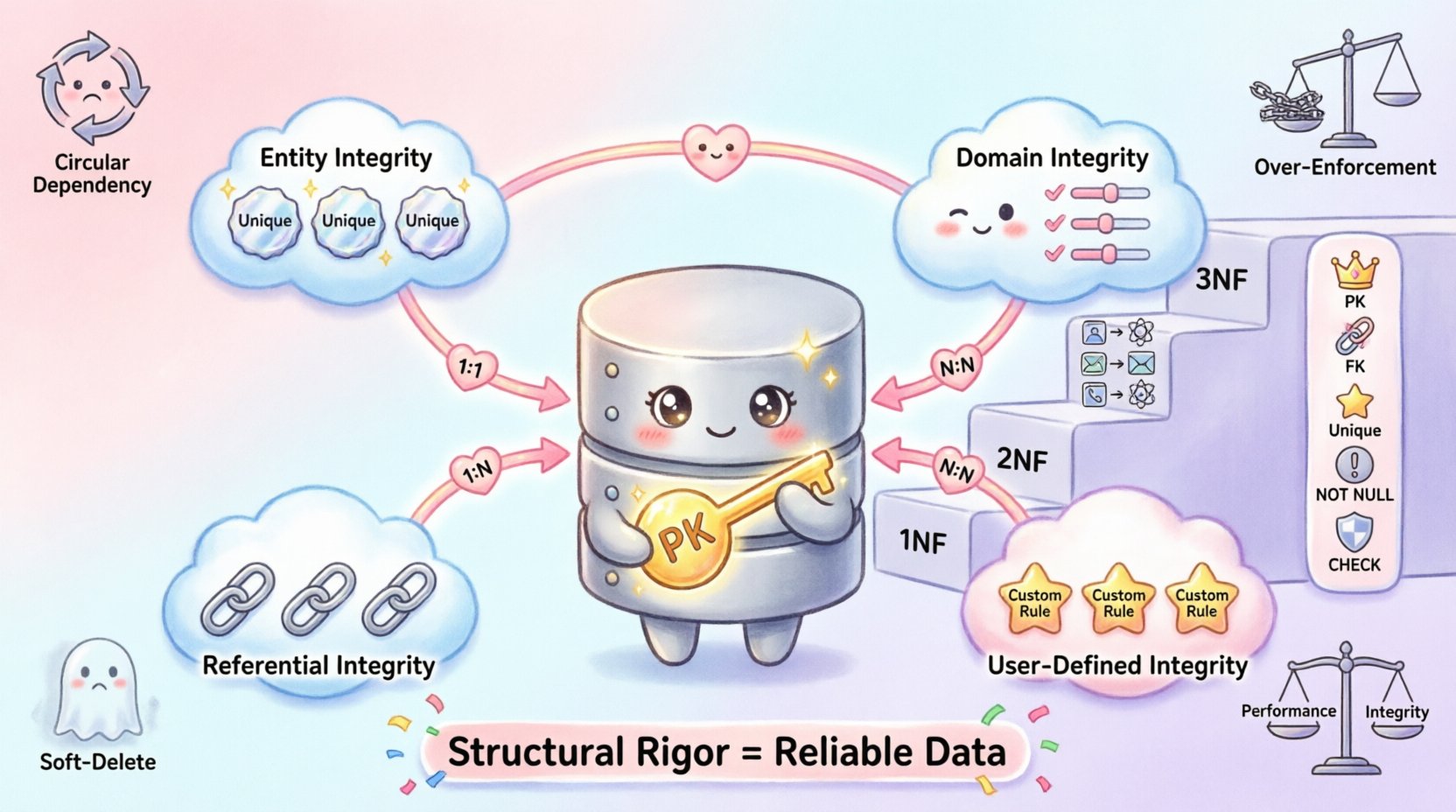
Integrity is not a single concept but a collection of rules that apply at different levels of the database structure. Recognizing these layers allows for targeted constraint implementation.
1. Entity Integrity
Entity integrity ensures that every row in a table is uniquely identifiable. This is the most fundamental requirement for any relational model. Without unique identification, tracking changes or relationships becomes impossible.
- Primary Keys: A column or set of columns designated as the unique identifier for a record.
- Not Null: The primary key column cannot contain null values, ensuring every record exists.
- Uniqueness: No two rows can share the same primary key value.
2. Domain Integrity
Domain integrity restricts the values that can be placed in a specific column. This ensures data remains within expected parameters, such as types, ranges, or formats.
- Data Types: Ensuring a column for age stores only integers, not text.
- Check Constraints: Validating that a value falls within a specific range, like a percentage between 0 and 100.
- Default Values: Providing a fallback value if none is supplied during insertion.
3. Referential Integrity
This ensures that relationships between tables remain consistent. If a record in one table points to another, the target record must exist. This prevents orphaned records that reference non-existent data.
- Foreign Keys: A column that links to the primary key of another table.
- Cascading Rules: Defining actions (delete or update) when the parent record changes.
- Null Handling: Deciding if a relationship can be optional (null) or mandatory.
4. User-Defined Integrity
These are business-specific rules that do not fit standard categories. They often require custom logic within the design or application layer.
- Custom Validation: Ensuring a date is not in the future.
- Conditional Logic: If a status is “Cancelled,” then no other payment records are allowed.
Core ERD Constraints and Their Impact 🧱
The ERD visualizes these constraints, making them visible to developers and stakeholders. The following table outlines common constraints, their purpose, and their effect on data consistency.
| Constraint Type | Function | Enforcement Point |
|---|---|---|
| Primary Key | Uniquely identifies rows | Table Definition |
| Foreign Key | Links tables together | Relationship Line |
| Unique | Prevents duplicate values in a column | Column Definition |
| Not Null | Requires a value for the field | Column Definition |
| Check | Validates value against a condition | Column or Table Definition |
When these constraints are properly defined in the design, the underlying database engine enforces them automatically. This removes the burden of validation from the application code, reducing the risk of bugs and security vulnerabilities.
Relationship Cardinality and Integrity 🔄
The lines connecting entities in an ERD represent relationships. The cardinality of these relationships dictates the strictness of the integrity rules required.
One-to-One Relationships
This occurs when a record in Table A matches exactly one record in Table B. It is common for splitting large tables for security or performance.
- Constraint: Both sides typically enforce uniqueness on the foreign key.
- Example: A Person and their Passport. One person has one passport; one passport belongs to one person.
One-to-Many Relationships
The most common relationship type. One record in Table A can be associated with multiple records in Table B.
- Constraint: The foreign key resides in the “Many” side table.
- Integrity: The foreign key must reference an existing primary key in the “One” side table.
- Example: A Customer and their Orders. One customer has many orders; an order belongs to one customer.
Many-to-Many Relationships
This requires a junction table to resolve the relationship into two one-to-many connections.
- Constraint: The junction table contains composite primary keys or unique constraints to prevent duplicate associations.
- Integrity: Prevents circular data or redundant entries in the linking table.
- Example: Students and Courses. A student takes many courses; a course has many students.
Normalization and Data Consistency 📐
Normalization is the process of organizing data to reduce redundancy and improve integrity. While often viewed as a performance optimization, it is primarily a data integrity strategy.
First Normal Form (1NF)
Ensures that each column contains atomic values. No lists or arrays within a single cell.
- Benefit: Simplifies querying and ensures consistent data types.
- Violation Risk: Storing multiple phone numbers in one field makes updating a single number difficult.
Second Normal Form (2NF)
Requires the table to be in 1NF and all non-key attributes to be fully dependent on the primary key.
- Benefit: Eliminates partial dependencies.
- Violation Risk: Storing customer address details in an Order table creates redundancy if the customer moves.
Third Normal Form (3NF)
Requires the table to be in 2NF and no transitive dependencies.
- Benefit: Ensures attributes depend only on the key.
- Violation Risk: Storing a city name in a customer table when that city is determined by a postal code (which determines the city) creates update anomalies.
Implementation Strategies for Robust Design 🛠️
Applying these concepts requires a disciplined approach during the modeling phase. The following strategies help maintain high integrity standards.
- Explicit Naming Conventions: Use clear names for foreign keys (e.g.,
user_idinstead offk1) to make relationships obvious during code reviews. - Documentation: Annotate the ERD with business rules. A constraint without context is hard to maintain.
- Validation Before Creation: Review the design for potential orphaned records before schema migration.
- Disable Constraints Temporarily: Only disable integrity checks during bulk data loads, and re-enable them immediately after to verify data quality.
- Audit Trails: Log changes to critical integrity fields to track who altered the data and when.
Common Pitfalls in Constraint Management ⚠️
Even with a solid plan, errors occur. Recognizing common mistakes helps avoid them.
1. Circular Dependencies
Creating a situation where Table A depends on Table B, and Table B depends on Table A. This creates a deadlock during table creation.
- Solution: Create tables without the foreign key constraint first, then add the constraint after both exist.
2. Over-Enforcement
Applying strict constraints where flexibility is needed. This can hinder legitimate business operations.
- Solution: Use nullable foreign keys for optional relationships and handle validation in the application layer if complex logic is required.
3. Ignoring Soft Deletes
Using a DELETE command removes data permanently, breaking referential integrity for historical records.
- Solution: Implement a
is_deletedboolean flag instead of physical deletion for critical historical data.
4. Performance vs. Integrity Trade-offs
Excessive constraints can slow down write operations. Every insert must check every rule.
- Solution: Index foreign keys to speed up lookups. Balance the need for real-time validation against system throughput requirements.
Maintaining Integrity Over Time 🔄
Data integrity is not a one-time setup. As business requirements evolve, the schema must adapt without compromising existing data.
- Schema Versioning: Treat database changes as code. Version control allows for rollback if a constraint breaks the system.
- Migration Testing: Run migration scripts in a staging environment that mirrors production data volumes.
- Periodic Audits: Run queries to find orphaned records that might have slipped through due to bugs or direct access.
- Backup Strategies: Regular backups ensure that if integrity is compromised, a clean state is available for recovery.
Final Thoughts on Structural Rigor 🎯
Building a system with strong data integrity requires foresight and discipline. The ERD serves as the primary tool for communicating these rules to the entire development team. By enforcing constraints at the database level, organizations reduce the complexity of application logic and increase confidence in their data.
Every constraint added is a guardrail. They prevent the system from veering off course. While they may seem restrictive during the design phase, they provide the necessary stability for long-term growth. Prioritizing these rules ensures that the data remains a reliable asset rather than a liability.
Adopting these practices creates a resilient architecture capable of withstanding the complexities of modern data processing. The result is a system where accuracy is built-in, not added on.