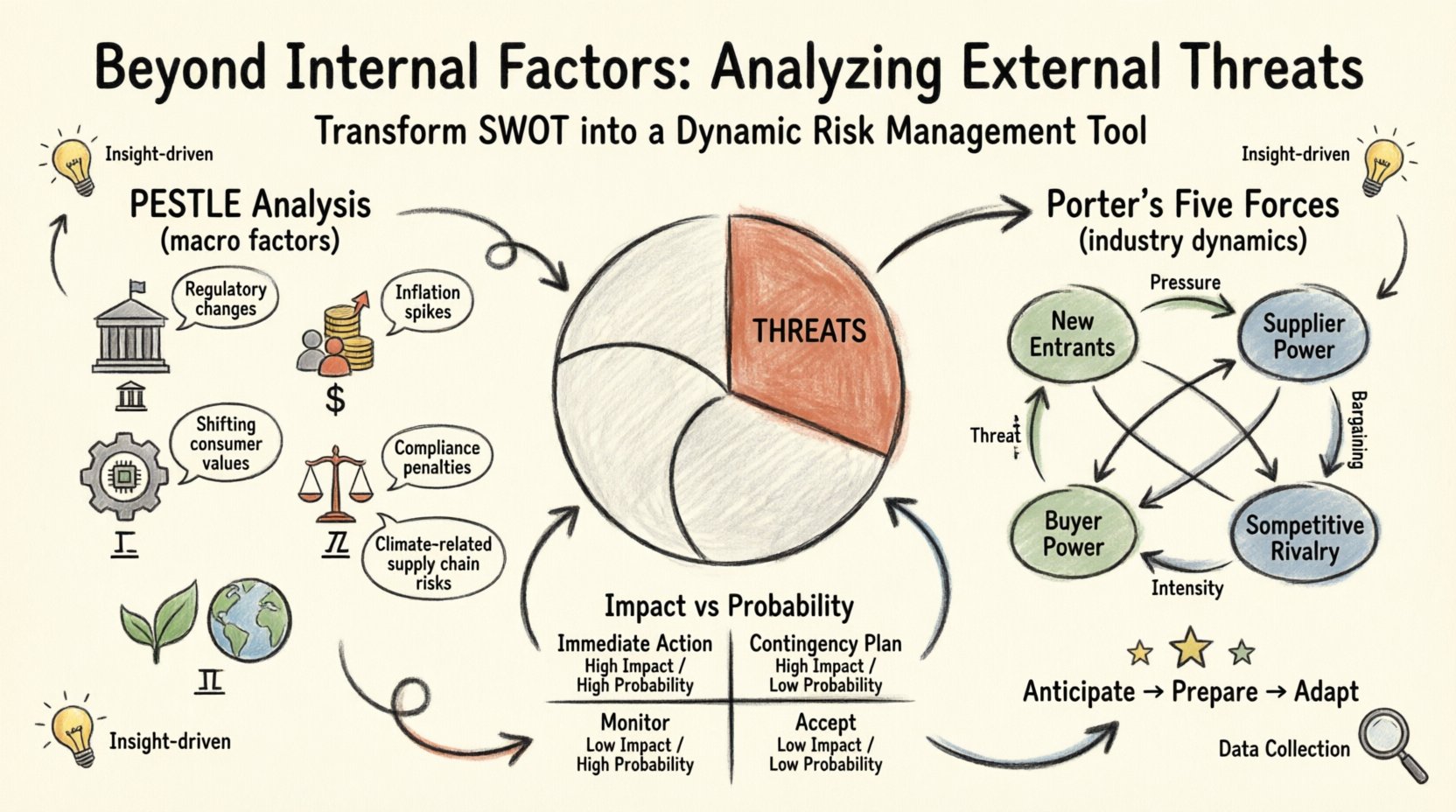
Strategic planning is often an exercise in introspection. Organizations look inward to assess their strengths and weaknesses. However, a SWOT analysis that focuses solely on internal capabilities leaves a business vulnerable to the unpredictable forces operating outside its walls. The Threats quadrant is frequently neglected or treated as a generic list of bad things. To truly secure a competitive position, you must move beyond internal factors and rigorously analyze external threats.
This guide provides a structured approach to identifying, categorizing, and mitigating external risks. By understanding the landscape outside your organization, you transform your SWOT from a static document into a dynamic risk management tool. We will explore frameworks, specific threat categories, and practical methods for gathering this intelligence without relying on proprietary software.
Understanding the External Environment 🌍
External threats are factors outside your organization that could cause trouble for business operations. Unlike weaknesses, which are internal deficiencies you can fix, threats are often beyond your direct control. You cannot force a competitor to lower their prices, nor can you dictate new government regulations. Your goal is not to control these factors, but to anticipate them and prepare responses.
Many teams make the mistake of listing specific competitors as the only threat. While competition is vital, the external environment is broader. It includes macroeconomic shifts, technological disruptions, and regulatory changes. A comprehensive analysis requires a panoramic view.
Why External Analysis is Critical
- Proactive vs. Reactive: Identifying threats early allows for strategic preparation rather than fire-fighting when a crisis hits.
- Resource Allocation: Knowing where the risks lie helps prioritize budget and personnel toward high-impact areas.
- Strategic Alignment: It ensures your strengths are aligned with market realities, preventing the deployment of resources into declining sectors.
- Investor Confidence: Demonstrating a clear understanding of external risks builds trust with stakeholders and partners.
Framework 1: PESTLE Analysis for Macro Factors 📊
One of the most effective methods for analyzing external threats is the PESTLE framework. It breaks down the macro-environmental factors into six distinct categories. This structure ensures you do not overlook a specific dimension of the market.
Political Factors 🏛️
Political stability and government policy significantly impact business operations. Threats in this category often relate to changes in leadership, trade restrictions, or taxation policies.
- Regulatory Changes: New laws regarding data privacy, labor, or environmental compliance can increase operational costs.
- Trade Barriers: Tariffs or import/export restrictions can disrupt supply chains.
- Political Instability: Unrest in key markets can lead to asset loss or operational shutdowns.
Economic Factors 💰
Economic conditions dictate the purchasing power of your customers and the cost of capital. Economic threats are often cyclical but can be sudden.
- Inflation: Rising costs of raw materials or labor can erode profit margins.
- Interest Rates: Higher rates increase the cost of borrowing for expansion or working capital.
- Exchange Rates: Fluctuations can affect the cost of imported goods or revenue from foreign markets.
- Recession: A downturn reduces overall demand for non-essential goods and services.
Social Factors 👥
Societal trends shape consumer behavior and workforce expectations. Ignoring these shifts can lead to brand irrelevance.
- Demographic Shifts: An aging population or changing migration patterns alter the talent pool and customer base.
- Consumer Values: Shifts toward sustainability or ethical sourcing can make outdated practices liabilities.
- Lifestyle Changes: Remote work trends or health consciousness can disrupt traditional business models.
Technological Factors 📱
Technology is often the most disruptive force. It creates opportunities, but also significant threats to those who fail to adapt.
- Obsolescence: Rapid innovation can render existing products or services obsolete overnight.
- Cybersecurity Risks: Increasing sophistication of attacks threatens data integrity and reputation.
- Automation: Competitors using advanced automation may undercut pricing or improve efficiency significantly.
- Disruption: New entrants using novel technologies can bypass traditional industry barriers.
Legal Factors ⚖️
Legal constraints operate alongside political factors but focus specifically on statutes and litigation.
- Compliance Costs: Adhering to industry-specific regulations requires investment in systems and training.
- Litigation: Intellectual property disputes or class action lawsuits can drain resources.
- Labor Laws: Changes in minimum wage or union regulations affect workforce management.
Environmental Factors 🌱
Environmental concerns are increasingly central to business continuity and reputation.
- Climate Change: Extreme weather events can disrupt supply chains and physical operations.
- Resource Scarcity: Limited access to water or energy sources impacts production.
- Waste Management: Stricter rules on waste disposal can increase operational overhead.
Framework 2: Porter’s Five Forces for Industry Dynamics 🔍
While PESTLE covers the macro environment, Porter’s Five Forces focuses on the immediate industry landscape. This framework helps identify the competitive intensity and profitability of your specific sector.
1. Threat of New Entrants 🚪
How easy is it for new competitors to enter your market? Low barriers to entry create a constant threat of price wars and market saturation.
- Capital Requirements: Low startup costs invite more competition.
- Regulatory Hurdles: Fewer licenses needed means easier market access.
- Brand Loyalty: Weak customer loyalty allows new players to steal market share quickly.
2. Bargaining Power of Suppliers 🤝
If your suppliers are powerful, they can dictate prices and terms, squeezing your margins.
- Supplier Concentration: If there are few suppliers, they hold more power.
- Switching Costs: High costs to change suppliers make you dependent on current vendors.
- Substitute Inputs: Lack of alternative materials increases supplier leverage.
3. Bargaining Power of Buyers 🛒
Customers with high bargaining power can demand lower prices or better quality, reducing your profitability.
- Price Sensitivity: Customers who are highly sensitive to price changes pose a threat.
- Volume Purchases: Large buyers can negotiate significant discounts.
- Product Differentiation: If your product is commoditized, buyers can easily switch.
4. Threat of Substitute Products 🔄
Substitutes are not direct competitors but alternative solutions to the same problem.
- Price-Performance Ratio: If a substitute offers better value, customers will switch.
- Switching Costs: Low costs to switch to an alternative increase the threat.
- Convenience: If a substitute is more convenient, it captures market share.
5. Competitive Rivalry 🥊
The intensity of competition determines how much effort is required to maintain market position.
- Number of Competitors: More competitors lead to more aggressive tactics.
- Industry Growth: Slow growth forces companies to fight for existing market share.
- Product Homogeneity: Similar products lead to price-based competition.
Identifying Specific Market Risks 📉
Beyond frameworks, specific types of threats often plague organizations. Categorizing these helps in assigning ownership for mitigation strategies.
Supply Chain Vulnerabilities
- Reliance on a single geographic region for manufacturing.
- Dependency on a sole-source vendor for critical components.
- Logistics bottlenecks during global disruptions.
Financial Instability
- High debt-to-equity ratios limiting flexibility.
- Exposure to volatile currency markets.
- Liquidity issues during seasonal downturns.
Reputational Risks
- Negative social media sentiment spreading rapidly.
- Associations with controversial partners or suppliers.
- Data breaches leading to loss of customer trust.
Competitive Threat Analysis 🏆
Competitors are the most visible external threat. However, analysis must go beyond what they are doing today and look at what they could do.
Direct Competitors
These are businesses offering similar products to the same customer base. Analyze their pricing, marketing spend, and product roadmaps.
- Are they launching a new feature that makes yours obsolete?
- Are they acquiring smaller firms to gain market share?
- Is their distribution channel expanding into your territory?
Indirect Competitors
These companies solve the same problem differently. For example, a video conferencing company competes with airlines for business travel time.
- Identify alternative solutions customers might choose instead of your core product.
- Monitor industries adjacent to yours for innovation that could spill over.
- Assess if customer habits are shifting toward these indirect solutions.
New Market Entrants
Startups and large conglomerates entering your space can disrupt established hierarchies.
- Watch for venture capital funding in your sector.
- Monitor patent filings from non-traditional players.
- Track hiring trends in your industry to spot emerging startups.
Data Collection and Monitoring Strategies 📋
How do you gather this information without expensive tools? The process relies on diligence, observation, and structured inquiry.
Primary Research Methods
- Customer Interviews: Ask clients what concerns them about the market or competitors.
- Supplier Conversations: Suppliers often know about industry shifts before they hit the news.
- Employee Feedback: Front-line staff often hear rumors or see trends first.
Secondary Research Sources
- Industry Reports: Look for white papers and market research from reputable firms.
- Financial Statements: Analyze the annual reports of public competitors to gauge their strategy.
- Government Publications: Census data, trade statistics, and regulatory filings are public resources.
- News Aggregators: Set up alerts for key terms related to your industry and competitors.
Integrating Threats into Strategy 💡
Identifying a threat is only the first step. The value comes from translating that insight into action. A threat in your SWOT must be paired with a potential response.
Scenario Planning
Develop scenarios based on the most severe threats. What happens if the supply chain breaks? What if a new regulation passes? Create contingency plans for each.
Mitigation vs. Acceptance
- Mitigation: Take action to reduce the probability or impact of the threat. Example: Diversifying suppliers.
- Acceptance: Acknowledge the threat exists but decide the cost of mitigation is too high. Example: Accepting minor currency fluctuations.
- Transfer: Shift the risk to a third party. Example: Purchasing insurance or outsourcing.
- Exploitation: Turn a threat into an opportunity. Example: If a competitor exits the market, acquire their customers.
Common Pitfalls in External Analysis ⚠️
Even with the right frameworks, teams often stumble when analyzing external threats. Avoid these common errors to ensure accuracy.
Vague Threat Definitions
Avoid listing threats like “Economic Downturn” or “Competition.” Be specific.
- Bad: “Inflation might rise.”
- Good: “Raw material costs may increase by 15% due to supply shortages.”
Ignoring Weak Signals
Focus on headlines, but also watch for faint signals. A small regulatory change in one country might be the precursor to a global shift.
Internal Bias
Do not dismiss threats because they contradict your internal narrative. If your team is optimistic, they may underestimate external risks. Encourage dissenting opinions during the analysis.
One-Off Exercise
SWOT analysis should not be an annual event. External threats evolve rapidly. Establish a routine for updating your threat landscape quarterly or monthly.
Table: Threat Impact vs. Probability Matrix 📉
Use this matrix to prioritize which threats require immediate attention and which can be monitored.
| Probability | Low Impact | High Impact |
|---|---|---|
| High | Monitor Manage routine issues. |
Immediate Action Top priority. Requires mitigation plan. |
| Low | Accept Ignore or minimal tracking. |
Contingency Plan Prepare response, but do not panic. |
Conclusion
External threats are the silent killers of strategic plans. While internal strengths determine what you can do, external threats determine what you must survive. By systematically applying frameworks like PESTLE and Porter’s Five Forces, and maintaining a disciplined approach to data collection, you can navigate uncertainty with confidence.
Remember that the goal is not to eliminate all risk, but to understand it well enough to manage it. Integrate this analysis into your regular strategic cycles. Keep the list of threats alive, review it frequently, and ensure that your response plans are actionable. This discipline transforms external uncertainty from a danger into a manageable variable in your business equation.